For decades, passwords have reigned supreme as the gatekeepers to our digital lives. However, the tides are turning. Security breaches, phishing attacks, and the sheer inconvenience of remembering countless logins have paved the way for a more secure and user-friendly alternative: Google Passkeys.
Bidding Farewell to Passwords: The Rise of Google Passkeys
This article delves into the world of Google Passkeys, exploring their functionalities, benefits, and potential to revolutionize the way we access online accounts.
Beyond Passwords: Unveiling the Power of Passkeys
Passkeys are cryptographic credentials that securely store login information without relying on traditional passwords. They leverage the capabilities of your devices, acting as unique digital keys paired with specific websites or applications.
Here’s how it works:
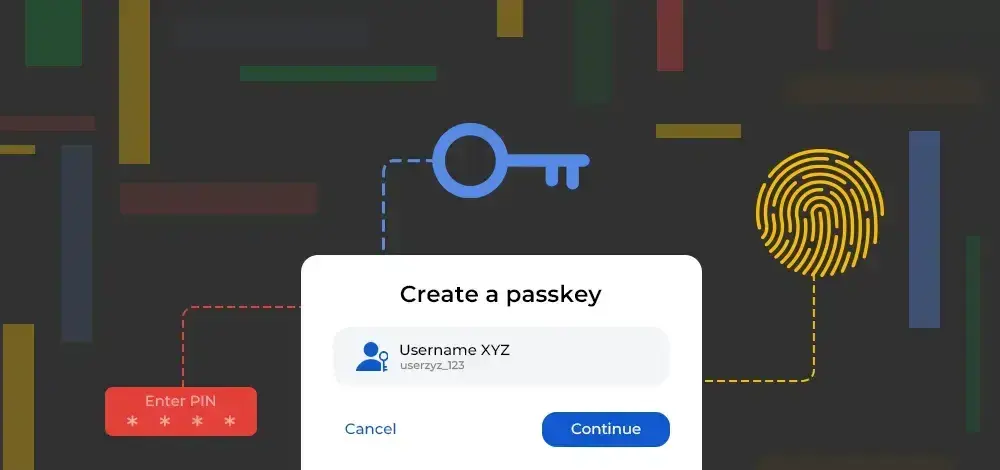
- Creation: When prompted to create a passkey on a website, your device (phone, computer) generates a public-private key pair. The public key is shared with the website, while the private key is securely stored on your device using biometric authentication (fingerprint, face scan) or a PIN.
- Authentication: During future login attempts, the website sends a request to your device, initiating the authentication process. You confirm your identity using your biometric method or PIN, and your device utilizes the private key to verify and grant access.
Advantages of Google Passkeys: A User-Centric Approach
The shift from passwords to passkeys offers a multitude of advantages:
- Enhanced Security: Passkeys are significantly more robust than passwords. They eliminate the risk of phishing attacks, as they do not require entering any information on the website itself. Additionally, they are not susceptible to brute-force attacks, as they are not based on guessable strings of characters.
- Convenience: Gone are the days of struggling to remember complex passwords. With passkeys, you simply use your preferred biometric authentication method or PIN, streamlining the login process.
- Cross-Platform Compatibility: Passkeys are built on open standards, ensuring compatibility across different operating systems and browsers. This eliminates the need for remembering separate logins for various devices and platforms.
- Multi-factor Authentication (MFA) Simplified: Passkeys inherently incorporate two-factor authentication (2FA) since they utilize your device and biometric data. This eliminates the need for separate one-time codes or security questions, further improving security and convenience.
- Reduced Reliance on Third-Party Authenticators: Passkeys alleviate the reliance on external authenticator apps, which can be cumbersome to manage and vulnerable to breaches.
Implementing Google Passkeys: A Glimpse into the Future
Also, Google is at the forefront of the passkey revolution, actively integrating this technology into its ecosystem. Here’s what you can expect:
- Sign in to your Google Account: You can now create and utilize passkeys for your Google Account. Simplifying and securing access to Gmail, Drive, YouTube, and other Google services.
- Support for Third-Party Applications: Google is actively working with developers to enable passkey support for a wide range of third-party applications and websites. This will expand the use of passkeys beyond Google services and create a more seamless experience across the web.
- Integration with Android and Chrome: Google Passkeys are seamlessly integrated with Android devices and Chrome browsers. Allowing for a smooth and intuitive user experience.

The Road Ahead: Challenges and Opportunities
While Google Passkeys hold immense potential, there are some challenges to overcome:
- Widespread Adoption: Achieving widespread adoption is crucial for passkeys to reach their full potential. This requires collaboration between tech companies, websites, and users to create a unified and standardized approach.
- Device Compatibility: Although Google Passkeys are designed to be cross-platform, ensuring compatibility with older devices and less commonly used operating systems is essential.
- User Education and Awareness: Educating users about the benefits and functionalities of passkeys is paramount for fostering trust and promoting their adoption.
Despite these challenges, the opportunities presented by Google Passkeys are undeniable. By embracing this technology, we can move towards a more secure, convenient, and future-proof way of managing online access.
Ushering in a New Era of Secure and Seamless Logins
So, the emergence of Google Passkeys marks a significant shift in the way we interact with the digital world. By leveraging the power of cryptography and biometrics, passkeys offer a robust and user-friendly alternative to passwords. As adoption grows and potential challenges are addressed, we can expect a future where secure and seamless logins become the norm, empowering us to navigate the online landscape with greater confidence and ease.
Beyond the Basics: Exploring Advanced Features and Future Prospects of Google Passkeys
The previous section explored the core functionalities and benefits of Google Passkeys. However, there’s more to this story than meets the eye. Let’s delve deeper into some advanced features and explore the exciting possibilities that Google Passkeys hold for the future.
Advanced Features:
- FIDO Compatibility: Google Passkeys are built on the FIDO (Fast Identity Online) standard, ensuring interoperability with other FIDO-compliant authenticators and password managers. This allows users to potentially manage their passkeys through existing tools they already trust.
- Platform Biometrics: Google Passkeys integrate seamlessly with platform-specific biometric authentication methods, such as Windows Hello on Windows devices or Face ID on Apple devices. This further enhances convenience and familiarity for users across different platforms.
- Password Import: Google Passkeys offer the ability to import existing passwords, easing the transition from password-based logins to a more secure and streamlined approach.
- Phishing Resistance: As mentioned earlier, passkeys offer inherent protection against phishing scams. Since users don’t enter any login information on suspicious websites, the risk of falling victim to these attacks significantly reduces.
Future Prospects:
So, looking ahead, several exciting possibilities lie at the horizon for Google Passkeys:
- Offline Authentication: Imagine a future where you can access your favorite online accounts even without an internet connection. This could be achieved by storing a backup copy of your passkeys locally on your device. Allowing for offline access in specific scenarios.
- Improved Security Measures: Continuous advancements in cryptographic technology can further enhance the security of passkeys. Making them even more resistant to potential threats in the evolving digital landscape.
- Enhanced User Experience: The user experience surrounding passkeys could continue to evolve. Potentially leading to features like one-tap logins and seamless synchronization across multiple devices, further streamlining the login process.
- Integration with Emerging Technologies: As technology continues to progress, Google Passkeys could potentially integrate with emerging technologies like virtual reality (VR) and augmented reality (AR), creating innovative login methods for future interactive experiences.

Gizchina News of the week
Beyond Google:
While Google is leading the charge, it’s important to remember that passkeys are not solely a Google initiative. Many other tech companies and organizations are actively developing and promoting this standard. This collaborative effort is crucial for ensuring widespread adoption and creating an ecosystem where passkeys can truly revolutionize online security and user experience.
Privacy Considerations and Addressing Concerns: A Balanced Approach to Google Passkeys
While Google Passkeys offer a plethora of advantages, it’s essential to address potential privacy concerns and ensure a balanced approach to their implementation.
Privacy Considerations:
- Data Storage: Where are passkeys stored? While Google emphasizes the security of storing private keys on user devices, some individuals might express concerns about potential vulnerabilities or breaches on personal devices.
- Biometric Data: Passkeys leverage biometric data like fingerprints or facial scans. The question of who has access to this data and how it’s used requires transparent communication and robust safeguards to ensure user trust.
- Single Point of Failure: Could relying solely on passkeys create a single point of failure if a device is lost or compromised? Backup and recovery options need to be carefully considered and communicated clearly to users.
Addressing Concerns:
- Transparency and Education: Open communication and user education are crucial. Google should clearly articulate how passkeys work, where they store the data, and how potential risks are mitigated.
- User Control: Users should retain control over their data and have the option to disable or delete their passkeys if they wish. This empowers individuals to make informed decisions about their online security.
- Regulatory Landscape: Collaboration with regulatory bodies is essential to ensure compliance with relevant data privacy regulations and build user trust in the adoption of passkeys.
Beyond Security: Societal and Ethical Implications
So, the discussion surrounding Google Passkeys extends beyond technical aspects and delves into broader societal and ethical considerations:
- Digital Inclusion: How can we ensure that everyone has equal access to the benefits of passkeys? considering potential barriers related to technology accessibility and literacy?
- Digital Divide: While passkeys offer improved security, could their widespread adoption exacerbate the digital divide if certain demographics lack the necessary resources or technology to utilize them?
- Ethical Implications: As technology evolves, ethical discussions surrounding the use and management of biometric data for authentication purposes will continue to be crucial.
Moving Forward with Responsibility:
It’s imperative to acknowledge both the benefits and potential drawbacks of Google Passkeys. By fostering transparent communication, addressing user concerns, and considering the broader societal and ethical implications, we can ensure a responsible and inclusive approach to implementing this promising technology.
The Future of Authentication: Beyond Google Passkeys
While Google Passkeys are currently gaining traction, it’s important to recognize that they exist within a larger landscape of evolving authentication methods. Some of the areas to monitor include:
- Passwordless Authentication Alternatives: Other passwordless authentication options, such as security keys and SMS-based one-time codes, will still play a role in the future, offering alternative solutions for specific situations or user preferences.
- Multi-factor Authentication (MFA) Evolution: MFA will likely continue to evolve, becoming even more sophisticated and user-friendly. Potentially incorporating context-aware factors to enhance security while maintaining user convenience.
- Emerging Authentication Technologies: Continuous innovation in various fields, like biometrics and artificial intelligence, could lead to the development of entirely new and unforeseen authentication methods in the future.
Tips and Tricks for a Smooth Transition to Google Passkeys
So, as the world embraces Google Passkeys, here are some helpful tips and tricks for a smooth and secure transition:
Start:
- Update your software: Ensure you have the latest updates for your operating system and browser to guarantee optimal functionality and security with passkeys.
- Enable biometric authentication: Set up fingerprint or facial recognition on your devices, which is often used for passkey verification.
- Review existing passwords: Consider importing existing passwords into Google Password Manager for a centralized and secure way to manage both passwords and passkeys.
Using Google Passkeys:
- Choose strong and unique PINs: When creating PINs for passkeys, avoid using common numbers or easily guessable sequences.
- Be cautious of phishing attempts: Remember, you shouldn’t enter any login information on suspicious websites. Passkeys verify your identity directly through your device, eliminating the risk of phishing scams.
- Manage your passkeys wisely: Keep track of the websites and applications where you’ve created passkeys. Use the password manager or your device settings to manage and, if necessary, delete passkeys for services you no longer use.
Staying Informed:
- Follow Google’s updates: Stay informed about the latest developments regarding Google Passkeys by following Google’s official channels or security blogs.
- Seek reliable resources: Look for trustworthy sources of information about passkeys and online security practices.
- Engage in discussions: Actively participate in discussions about passkeys with friends, family, and online communities. Sharing knowledge and concerns can foster a more informed and secure online environment.
Additional Tips:
- Consider using a password manager: While Google Passkeys offer a secure and convenient solution, password managers can still be valuable for storing other types of sensitive information like login credentials for non-passkey-enabled websites and applications.
- Be mindful of device security: Maintain strong security practices on your devices, including using strong passwords or PINs. Keeping software updated, and implementing basic security measures like two-factor authentication when available.
- Educate others: Spread awareness about the benefits and responsible use of Google Passkeys to encourage a more secure online community.
By following these tips and tricks, you can confidently embrace Google Passkeys and contribute to building a more secure and user-friendly online experience for everyone. Remember, staying informed and adopting responsible practices are key to navigating the ever-evolving landscape of online security.
Via: gizchina.com